Have you ever needed to troubleshoot M3 API calls in Wireshark? Unfortunately, the M3 API protocol is a proprietary protocol. Consequently, Wireshark does not understand it, and it just gives us raw TCP data as a stream of bytes.
Abstract
I implemented a simple protocol dissector for Wireshark that understands the M3 API protocol, i.e. it parses the TCP stream to show the M3 API bytes in a human-readable format, with company (CONO), division (DIVI), user id (USID), and MI program (e.g. CRS610MI). The dissector is currently not complete and only parses the MvxInit request phase of the protocol.
Reverse engineering
I reverse engineered the M3 API protocol thanks to MvxLib, a free and open source client implementation of the protocol in C# by Mattias Bengtsson (now deprecated), and thanks to MvxSockJ, the official and closed-source client implementation of the protocol in Java (up-to-date).
MvxInit
The MvxInit phase of the protocol is the first phase of the protocol for connection and authentication, and it has the following structure:
struct MvxInit
{
struct request {
int size;
char Command[5]; // PWLOG
char CONO_DIVI[32];
char USID[16];
char PasswordCiphertext[16]; // password ^ key
char MIProgram[32]; // e.g. CRS610MI
char ApplicationName[32]; // e.g. MI-TEST
char LocalIPAddress[16];
};
struct response {
int size_;
char message[15];
};
};
Wireshark Generic Dissector
I used the Wireshark Generic Dissector (wsgd) to create a simple dissector. It requires two files: a data format description, and a file description.
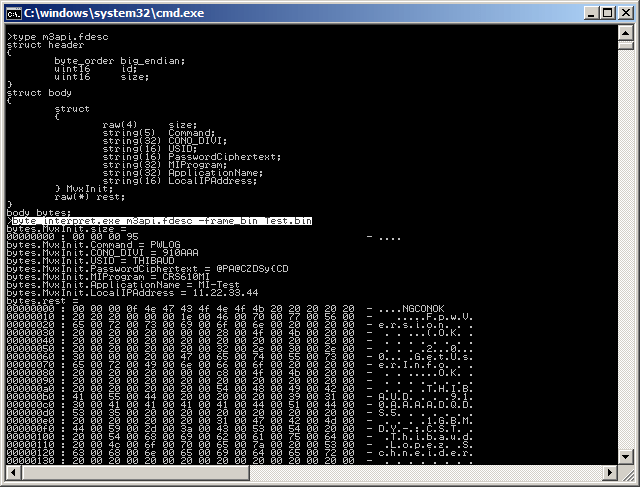
The data format description m3api.fdesc is very similar to the C struct above, where the header is required by wsgd:
struct header
{
byte_order big_endian;
uint16 id;
uint16 size;
}
struct body
{
struct
{
uint32 size;
string(5) Command;
string(32) CONO_DIVI;
string(16) USID;
string(16) PasswordCiphertext;
string(32) MIProgram;
string(32) ApplicationName;
string(16) LocalIPAddress;
} MvxInit;
}
Given the limitations of wsgd and its message identifier, I could not solve how to parse more than one type of message, so I chose the MvxInit request, and the rest will throw errors.
I made a test M3 API call to M3BE, I captured it in Wireshark, and I saved the TCP stream as a binary file (I anonymized it so I can publish it here):

Then, I used wsgd’s byte_interpret.exe (available on the wsgd downloads), using that test binary file, to fine tune my data format description until it was correct:
byte_interpret.exe m3api.fdesc -frame_bin Test.bin
Then, here is the wsgd file description m3api.wsgd; note how I listed the TCP port numbers of my M3 API servers (DEV, TST, PRD):
PROTONAME M3 API protocol PROTOSHORTNAME M3API PROTOABBREV m3api PARENT_SUBFIELD tcp.port PARENT_SUBFIELD_VALUES 16305 16405 16605 # DEV TST PRD MSG_HEADER_TYPE header MSG_ID_FIELD_NAME id MSG_SUMMARY_SUBSIDIARY_FIELD_NAMES size MSG_TOTAL_LENGTH size + 4 MSG_MAIN_TYPE body PROTO_TYPE_DEFINITIONS include m3api.fdesc;
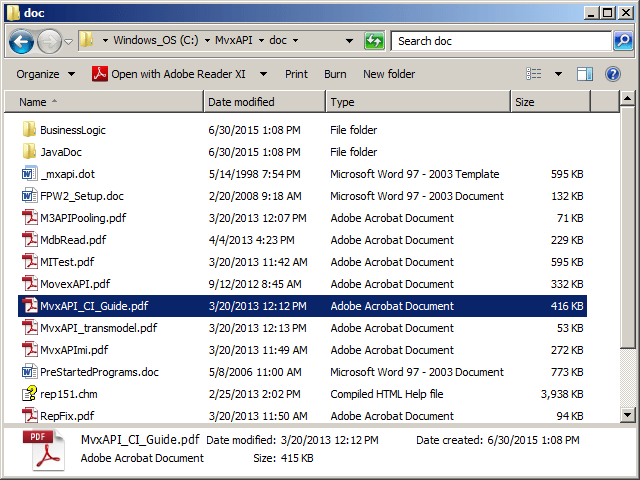
To activate the new dissector in Wireshark, simply drop the wsgd generic.dll file into Wireshark’s plugins folder, and drop the two above files into Wireshark’s profiles folder:

Then, restart Wireshark, and start capturing M3 API calls. Wireshark will automatically parse the TCP stream as M3 API protocol for the port numbers you specified in the data format description.
Result
Here is a resulting capture between MI-Test and M3BE. Note how you can filter the displayed packets by m3api. Note how the protocol dissector understands the phase of the M3 API protocol (MvxInit), the company (CONO), division (DIVI), user id (USID), and MIProgram (CRS610MI). Also, I wrote C code to decrypt the password ciphertext, but I could not solve where to put that code in wsgd, so the dissector does not decrypt the password.
Limitations and future work
- I am using M3BE 15.1.2. The M3 API protocol may be different for previous or future versions of M3.
- I am doing user/password authentication. The M3 API protocol supports other methods of authentication.
- Given the limitations of wsgd and its message identifier, I will most likely discontinue using wsgd.
- Instead, I would write a protocol dissector in LUA.
- Ideally, I should write a protocol dissector in C, but that is over-kill for my needs.
Conclusion
That was a simple M3 API protocol dissector for Wireshark that parses and displays M3 API bytes into a human readable format to help troubleshoot M3 API calls between client applications and M3 Business Engine.
About the M3 API protocolThe M3 API protocol is a proprietary client/server protocol based on TCP/IP for third-party applications to make API calls to Infor M3 Business Engine (M3BE). It was created a long time ago when Movex was on AS/400. It is a very simple protocol, lean, efficient, with good performance, it is available in major platforms (IBM System i, Microsoft Windows Intel/AMD, SUN Solaris, Linux, 32-bit, 64-bit, etc.), it is available in major programming languages (C/C++, Win32, Java, .NET, etc.), it supports Unicode, it supports multiple authentication methods, and it has withstood the test of time (since the nineties). It has been maintained primarily by Björn P. The data transits in clear text. The protocol had an optional encryption available with the Blowfish cipher, but that feature was removed. Now, only the password is encoded with a XOR cipher during MvxInit. If you need to make secure calls, use the M3 API SOAP or REST secure endpoints of the Infor Grid. For more information about M3 API, refer to the documentation in the M3 API Toolkit: |



UPDATE: I forgot to mention the following. Network byte order is Big Endian whereas Wintel computers byte order is Little Endian. In my test capture above, the MvxInit request size is hexadecimal 00 00 00 95 (decimal 149). In my C code above, the variable int size will be incorrectly read in the wrong byte order as hexadecimal 95 00 00 00. I convert it from Big Endian to Little Endian with the POSIX ntohl function (net-to-host-long), size = ntohl(size);
LikeLike
Do you have traffic capture for M3 protocol?
LikeLike